How Frequently Has T-Mobile Been Breached? An Awareness Analysis (2015–2025)

.jpg)
Introduction
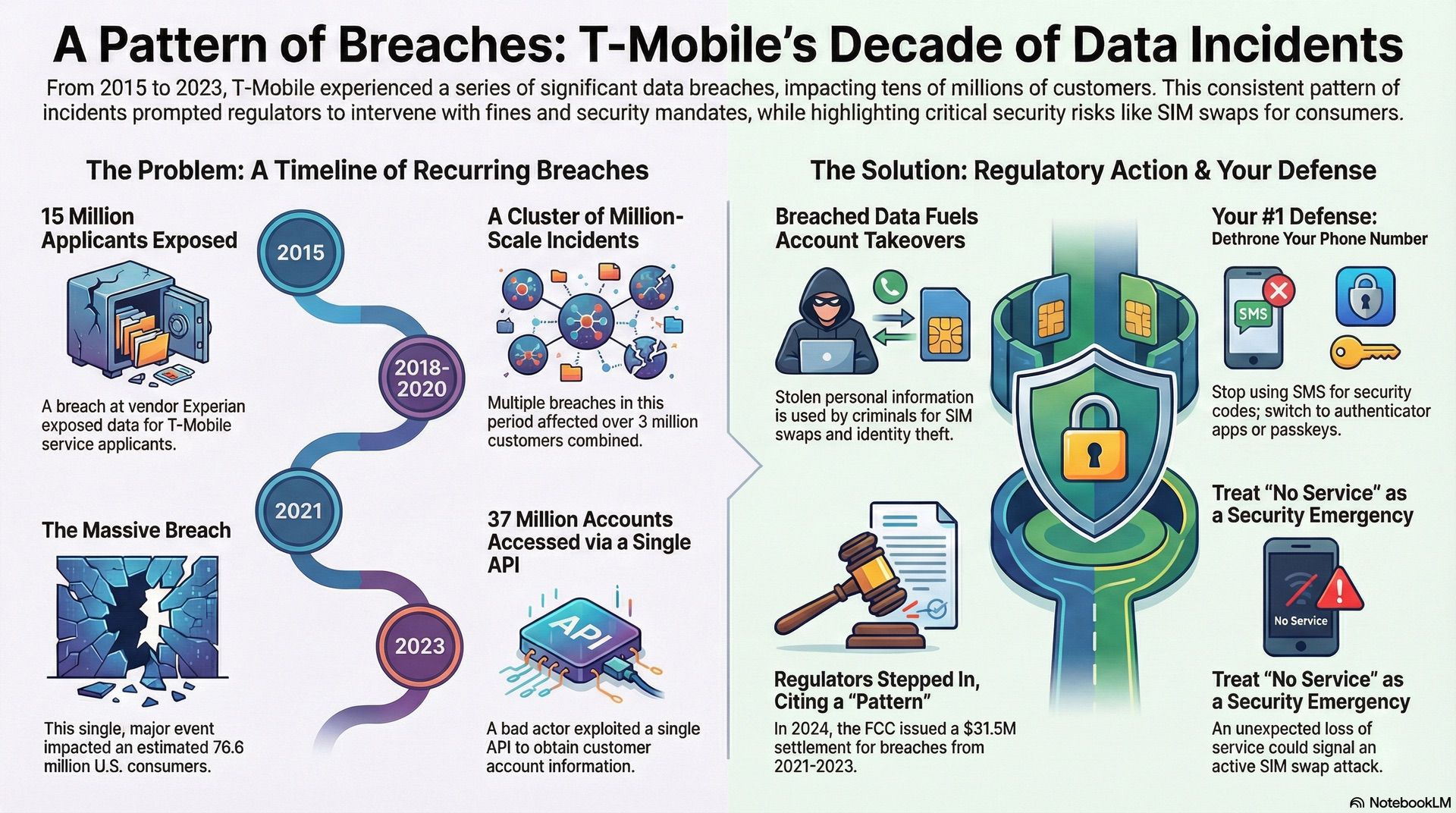
If it feels like T-Mobile shows up in breach headlines a lot, that’s because it has, especially from 2018 through early 2023.
Some were massive. Some were smaller. Together, they created a reputation problem that regulators eventually treated as systemic, not accidental.
Today, we’re counting incidents where T-Mobile (or a regulator, or a state AG filing) says a bad actor accessed customer or applicant data.
Is your cellphone vulnerable to SIM Swap? Get a FREE scan now!
Please ensure your number is in the correct format.
Valid for US numbers only!
The Quick Reality Check On Frequency
From 2015 through early 2023, there were multiple major, publicly disclosed incidents, including a vendor breach involving T-Mobile applicants, several million-scale customer incidents, and two separate disclosures in 2023.
Then in September 2024, the FCC and T-Mobile reached a $31.5 million settlement tied to breaches the FCC said occurred in 2021, 2022, and 2023, and it came with required security improvements under a consent decree.
You can see this covered in the Reuters report and in the FCC’s consent decree document.
So the short answer is: it has been frequent enough that regulators treated it as a multi-year pattern, not a one-off.
A Timeline Of Publicly Disclosed Incidents
This is the cleanest way to see “how often” without hand-waving.
2015: Vendor Breach Affecting T-Mobile Applicants
T-Mobile said the Experian breach involved about 15 million applicants who applied for service or device financing.
2018: Customer Data Breach Around 2 Million People
T-Mobile disclosed a breach impacting roughly 2 million customers in August 2018.
2019: Prepaid Customer Breach Over 1 Million
In November 2019, reporting and breach notice coverage described a breach affecting more than 1 million prepaid customers.
2020: Employee Email Accounts Compromised
T-Mobile disclosed a breach involving compromised employee email accounts in March 2020.
Late 2020 Into Early 2021: CPNI Incident
T-Mobile disclosed unauthorized access affecting approximately 200,000 customers involving CPNI type data.
2021: The Massive Breach
T-Mobile published updates during the investigation, including that about 850,000 prepaid account PINs were exposed.
Later, the FCC characterized the 2021 breach as impacting 76.6 million U.S. consumers.
2023: The “Single API” Incident Affecting 37 Million Accounts
T-Mobile said a bad actor used a single API to obtain limited account info, and Reuters summarized this event as impacting 37 million.
2023: A Separate Disclosed Incident Affecting 836 People
Maine’s AG breach portal lists a T-Mobile incident affecting 836 people.
What Changed In 2024 And 2025
Even if you ignore new “breach count” debates, the regulatory and real-world tail risk is still active.
Regulators Treated It As A Pattern
The FCC settlement and consent decree was explicitly framed around incidents in 2021, 2022, and 2023, which you can confirm in the FCC’s consent decree document and the related Reuters coverage.
Not All Headlines Are “Hacks,” Some Are Privacy Violations
In April 2024, the FCC fined carriers for location data practices, including an over $80 million fine for T-Mobile. You can see this in the FCC’s public announcement and the FCC’s order PDF.
A Lawsuit Landed In 2025
Washington’s AG filed a lawsuit in January 2025 tied to the 2021 breach and alleged security failures, affecting more than 2 million Washingtonians, as described in the AG’s press release.
The “New Breach” Claims Keep Happening Because Old Data Never Dies
In June 2025, Cybernews reported claims of 64 million records, while T-Mobile denied a new breach and outlets discussed the possibility of recycled or mixed datasets in coverage like this Tom’s Guide writeup.
T-Mobile Has Been Public About Security Investment
In October 2025, T-Mobile announced new security facilities, including a Cyber Defense and Executive Briefing Center initiative.
SIM Swap Protection
Get our SAFE plan for guaranteed SIM swap protection.
So How Frequent Is “Frequent,” In Plain English?
If you look at public disclosures:
There is a long gap early on (2015 to 2018).
Then there’s a clear cluster from 2018 through early 2023, including million-scale incidents in 2018, 2019, 2021, and 2023, plus smaller disclosures like the 836-person incident. You can verify those disclosures in the 2018 TechCrunch report, the 2019 TechCrunch report, the 2021 FCC scale framing in the 2024 Reuters report, the 2023 disclosure in T-Mobile’s own customer information update, and the small 2023 event in the Maine AG listing.
That “clustered” period is why the public perception is “this keeps happening.”
Monthly
Yearly
Why This Matters For SIM Swaps And Account Takeovers
Breach data is not just embarrassing PR. It is fuel.
Names, phone numbers, dates of birth, addresses, account details, and PIN related info are exactly the stuff attackers use for social engineering and account recovery abuse.
This is also why telecom access is valuable to criminals. Krebs reported claims that groups accessed T-Mobile internal tools in more than 100 incidents during 2022, often aiming to enable SIM swap style diversion of calls and texts, in this KrebsOnSecurity report.
Even if you never lost money directly from a breach, breached data increases your odds of getting hit later.
What You Should Do If You’re A T-Mobile Customer Or Former Customer
This is the part that actually changes your risk.
Stop Using SMS As Your Main Security Layer
If your important accounts still rely on SMS codes, a SIM swap can turn into an account takeover fast. Move to authenticator apps, passkeys, or hardware keys wherever possible.
Lock Your Carrier Account
Use every carrier-side protection feature available. Your carrier account should be locked down like it is your bank, because in practice it is a gateway to your bank.
Treat Any Sudden “No Service” As A Security Emergency
If your phone drops to “No Service” unexpectedly, assume SIM swap until proven otherwise.
Monitor Identity Exposure, Not Just Your Phone Bill
If you suspect your SSN or ID info may have been exposed in a past breach cycle, credit freezes and monitoring are often higher leverage than endlessly changing passwords.
The Bottom Line
If you want a clean answer to “how often,” it’s this:
Often enough that, from 2018 through early 2023, breaches became a recurring public issue, and serious enough that regulators stepped in with structural mandates in 2024.
If you want to reduce your personal risk, the most important shift is architectural, not emotional:
Stop letting your phone number be the key to your digital life.







