How a SIM Swap Scam Works, Step-by-Step Breakdown of the Attack

Introduction
Your phone signal drops to one bar, then to nothing. Just “SOS only”.
You reboot your phone, pull the SIM, put it back in. Still dead. While you are fighting with it, your email inbox starts filling up on your laptop:
- “Password changed successfully”
- “New device logged in to your bank account”
- “Your crypto withdrawal request is being processed”
You never typed any of this. But someone else did, using your phone number. That is a SIM swap scam in motion, and by the time most people realize it, the money is already gone.
This guide walks through how a SIM swap attack actually works, step by step, from the criminal’s point of view. The goal is not to turn you into a security engineer. It is to make you understand how fragile a normal phone plan is, and why you need serious SIM swap protection if you have anything worth stealing.
Is your cellphone vulnerable to SIM Swap? Get a FREE scan now!
Please ensure your number is in the correct format.
Valid for US numbers only!
What A SIM Swap Scam Really Is
A SIM swap scam, also called a SIM swap attack or SIM hijacking, is a type of account takeover where criminals convince a mobile carrier to move your phone number onto a SIM card they control. Once that happens, every call, text message, and one time password for two factor authentication goes to them instead of you.
From there they can reset passwords, approve logins, and break into almost any account tied to that number. Banks, crypto exchanges, email providers, social platforms, even work accounts still treat your mobile number as a trusted identity signal.
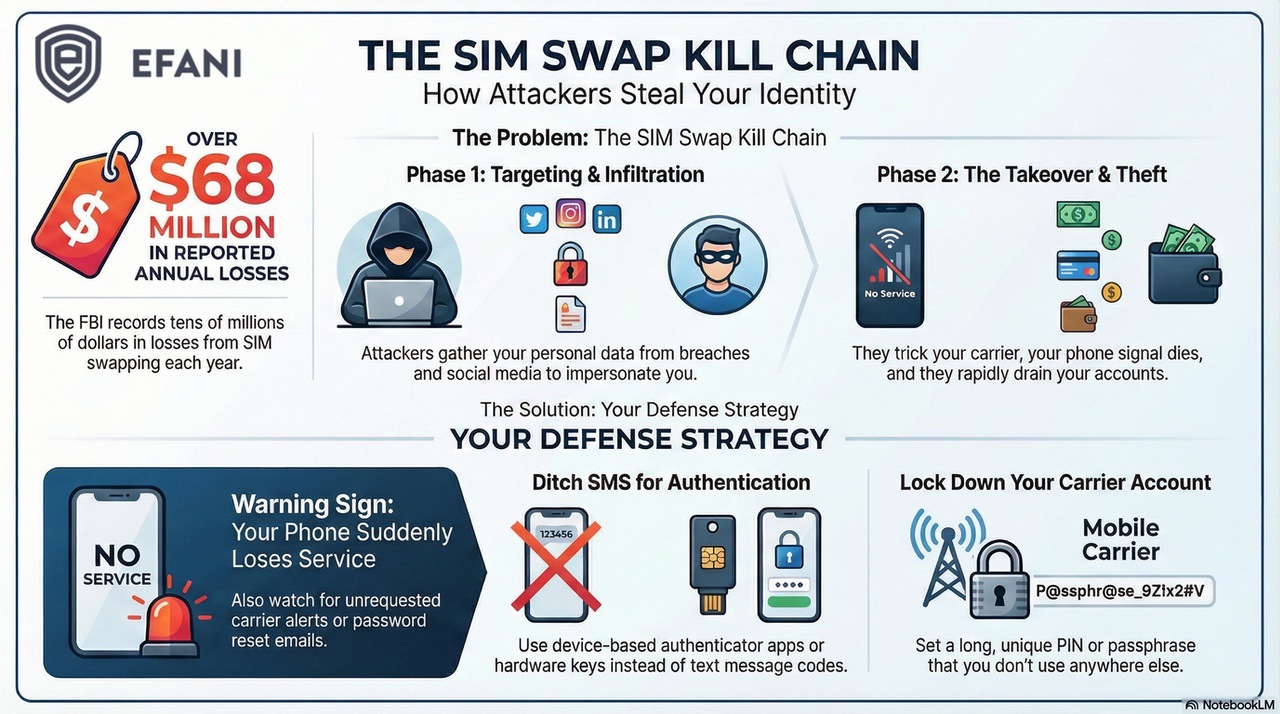
The scale of SIM swap fraud is not theoretical.
- The FBI’s Internet Crime Complaint Center recorded 1,611 SIM swapping complaints in 2021, with more than 68 million dollars in losses, and the trend has stayed high with tens of millions in losses each year since.
- In 2023 alone, the FBI investigated more than 1,000 SIM swap attacks that cost victims nearly 50 million dollars.
- One arbitration case against T Mobile over a SIM swap that led to stolen crypto ended in a 33 million dollar award for a single customer.
Criminals love this attack because it is high reward and relatively low tech. They do not need malware or zero day exploits. They just need data about you, a cooperative or careless carrier, and a short window of time.
Step By Step SIM Swap Scam Attack Lifecycle
Every SIM swap scam follows the same basic playbook. Different actors use different tools, but the structure is consistent.
Think of it as a five step kill chain.
Step One: Reconnaissance And SIM Swap Target Profiling
Before a criminal ever calls your carrier, they build a profile on you. They need enough personal data to impersonate you convincingly when a carrier rep asks security questions.
They pull this data from several places:
- Massive data breaches and dark web “fullz” packages that include your name, address, SSN, and old passwords
- Phishing emails or fake “bank” or “carrier” texts that trick you into handing over codes or login details
- Open source intelligence from social media, LinkedIn, and public records that expose dates of birth, family names, pet names, and other “secret” answers
Because high quality personal data is cheap and widely available, relying on basic PII for identity checks is no longer real security. For SIM swap fraud, this reconnaissance step is everything. If they can answer your carrier’s questions, the rest becomes routine.
Step Two: Carrier Manipulation And Social Engineering
Once the attacker has enough data, they move to the carrier. This is where most SIM swap scams either succeed or fail.
Typically the attacker calls customer support pretending to be you. They sound stressed but polite. They already have a script ready. Common stories include a lost phone, a broken phone, or “I just bought a new iPhone and need to move my number.”
Using your stolen data, they answer security questions, confirm your address, maybe read off the last four digits of your SSN. Some carriers still treat that as proof that you are the real customer. If the rep is rushed or poorly trained, the attacker wins.
In higher value scams, criminals do not even bother with scripts. They bribe or recruit insiders at carriers to perform the SIM swap from the inside. Investigations have repeatedly found telecom employees paid to run fraudulent swaps that led to large crypto thefts.
In both cases, the weakness is the same. A normal carrier treats a SIM change or port out as routine customer service, not as a critical security event.
Step Three: SIM Swap Provisioning When Your Phone Suddenly Dies
If the carrier approves the request, your number is “ported” or moved to a new SIM card or eSIM the attacker controls. This is the exact moment the SIM swap attack becomes real.
On your side, it looks boring at first:
- Your phone loses signal for no obvious reason
- Calls go straight to voicemail
- Texts stop arriving, even on Wi Fi
Most people assume it is a coverage glitch or a random outage and wait it out. That delay is exactly what the attacker wants. While you are rebooting your phone, they are already using your number.
From this point on, every SMS code and phone call intended for you lands on a device in the attacker’s hand. They now own your “telephony identity”.
Step Four: Rapid Account Takeover And Financial Theft
Once the SIM swap completes, the clock starts. Good attackers work fast. It often takes minutes, not hours, to do the damage.
A typical SIM swap fraud sprint looks like this:
- First they reset your primary email account using a “text me a code” recovery flow
- With that email under control, they reset logins for banks, brokerages, crypto exchanges, password managers, and cloud storage
- They intercept every SMS one time password that would normally protect those logins
- They add their own authenticator app or hardware key, then remove your old factors and recovery options
At that point they can drain accounts, sell your crypto, move funds through mixers, and even request new cards or loans in your name. Most victims do not realize what happened until they try to log in and find that their passwords, recovery email, and phone based 2FA are already changed.
Step Five: Cleanup, Lockout And Long Term Identity Fraud
The last step of a SIM swap scam is about persistence and cover. Once the money is moved, the attacker wants to stay a step ahead of you and any investigators.
Common moves include:
- Deleting alerts and messages in compromised email accounts so you do not see warnings
- Changing usernames or handles for social media to pivot into scams targeting your contacts
- Selling your identity data to other groups that specialize in tax refund fraud, loan fraud, or synthetic identities
In some cases, attackers even move your number back to your original SIM after they are done, to reduce suspicion. You get your service back, but your accounts and recovery options are already changed behind the scenes.
Why SIM Swap Attacks Break SMS 2-Factor Authentication
On paper, 2-factor authentication should stop account takeover. In reality, SMS based 2FA is exactly what SIM swap fraud is designed to bypass.
The core problem is that SMS codes are bound to your phone number, not to your physical device. A phone number is just an entry in a carrier database.
It can be moved to a different SIM with one successful social engineering call or one insider with access. When that happens, all those “extra security” codes flow straight to the attacker.
This is why security teams and regulators are increasingly warning that phone numbers should never be treated as a strong identity factor for high value accounts. Safer options include:
- Device based authenticator apps that generate codes locally
- Hardware security keys using FIDO2 or WebAuthn
- Passkeys tied to your device rather than your number
If your bank, exchange, or broker still insists on SMS codes for large transactions, you should treat your phone number as a single point of catastrophic failure.
SIM Swap Protection
Get our SAFE plan for guaranteed SIM swap protection.
Early Warning Signs Of A SIM Swap Attack
You cannot see the reconnaissance stage, but you can catch the moment the SIM swap begins if you know what to watch for.
Key warning signs include:
- Sudden loss of mobile service while people around you still have signal and you are not in a dead zone
- Texts or emails from your carrier about a SIM change, eSIM activation, or number transfer that you did not request
- Login alerts, password reset emails, or new device notifications for accounts you are not actively using
- Two factor codes arriving on your phone that you did not initiate
If two or more of these happen together, treat it as a SIM swap emergency, not a minor glitch.
Monthly
Yearly
How To Reduce Your SIM Swap Scam Risk
You cannot make yourself impossible to target, but you can make yourself a very expensive target. The goal is to remove the easy paths criminals rely on.
Start with basic hygiene that shrinks the attack surface:
- Move as many important logins as possible away from SMS codes and onto an authenticator app or hardware key
- Lock down social media and remove obvious answers to security questions, like your full birthdate and family details
- Use strong, unique passwords in a password manager so one breach does not unlock everything
- Set a long, random account PIN or passphrase with your carrier and never reuse it anywhere else
For higher risk people like executives, crypto investors, founders, and public figures, the second layer is your carrier choice. A standard mass market plan is designed for convenience, not for SIM swap protection. You want a secure mobile service that treats a SIM change like a bank treats a wire transfer.
How Efani Blocks SIM Swap Attacks At The Carrier Level
This is exactly why Efani exists. Our team built America’s most secure mobile service after being SIM swapped multiple times through mainstream carriers.
Instead of relying on basic PII and a rushed call center, Efani wraps your number in multiple layers of verification and default blocks. Our SAFE plan includes:
- An 11 layer proprietary authentication protocol for any sensitive change on your account
- Default SIM swap blocking and port out freezes so your number cannot move without going through a strict, human verified workflow
- A mandatory cooling off period on port outs as a last resort safety net in case everything else fails
- Up to 5 million dollars of insurance coverage for losses if a SIM swap somehow gets through
You still need secure habits and strong authentication on your bank, email, and crypto accounts. But with Efani acting as your carrier, you remove the easiest attack path most SIM swap criminals depend on.
Instead of one phone call standing between an attacker and your money, they face multiple checks, careful humans, and real financial consequences.
If your net worth, role, or business would be badly damaged by a SIM swap attack, upgrading to a secure cell phone service is not a luxury. It is part of basic risk management.
Conclusion
If you take one lesson away from this breakdown, make it this: a normal phone plan is not designed to protect your money, your crypto, or your reputation. SIM swap scams work because carriers treat your number as a customer service field, not as a critical identity key.
Change that assumption, and you change your risk. Move your important logins off SMS, clean up your digital footprint, and if you are in any kind of high risk category, put your number behind a secure carrier like Efani so that a stranger’s phone call cannot decide your financial future.
FAQs
Can A SIM Swap Scam Happen If My Phone Still Works?
In a classic SIM swap attack, your primary number moves off your SIM, so you lose normal service. That said, attackers sometimes test or partially change lines on multi line accounts, or target secondary numbers. If you see unexplained carrier emails or password reset activity even while your phone still appears normal, take it seriously and contact your carrier from a different device.
Do Hackers Need Physical Access To My Phone For A SIM Swap Attack?
No. That is one reason SIM swap fraud is so dangerous. The attacker does not need your phone, your SIM, or your face. They only need enough information to convince or bribe someone at your carrier to move your number to a SIM or eSIM they control. Everything else can be done remotely.
Are eSIMs Safe From SIM Swap Fraud?
eSIMs remove the physical plastic card, but they do not remove the core risk. Your number can still be reassigned inside the carrier’s systems if someone approves a transfer. Some carriers add extra checks around eSIM provisioning, but social engineering and insider abuse are still possible if the processes are weak. You still need strong SIM swap protection at the carrier level and better factors than SMS on your important accounts and this is where Efani can help you.







