Phishing Attacks Explained: Meaning, Methods, and How to Prevent Them


Introduction
If you have ever opened an email that made your stomach drop for half a second, you already understand phishing on a gut level.
It is that moment when a message looks just real enough to make you pause. A bank alert. A delivery notice. A password reset you do not remember requesting. A text saying your account is locked unless you act right now.
Phishing is one of the most common and effective cyber attacks in the world, not because it uses advanced hacking tricks, but because it targets people instead of systems. It relies on trust, urgency, and habit. And it works far more often than most people like to admit.
This guide breaks phishing down in plain language. What it is, how it works, the different forms it takes, why it is so effective, and how to spot and stop it before it causes real damage.
Is your cellphone vulnerable to SIM Swap? Get a FREE scan now!
Please ensure your number is in the correct format.
Valid for US numbers only!
What Phishing Is
Phishing is a type of cyber attack where someone pretends to be a trusted source to trick you into giving up sensitive information or taking a risky action.
That information might include:
- Login credentials like usernames and passwords
- One time passcodes or verification codes
- Credit card or banking details
- Personal data such as addresses, dates of birth, or ID numbers
The action might be clicking a malicious link, opening an infected attachment, or sending money to the wrong place.
The key thing to understand is this. In a phishing attack, you are not being hacked in the technical sense. You are being manipulated into opening the door yourself.
That is what makes phishing so dangerous.
How Phishing Attacks Work
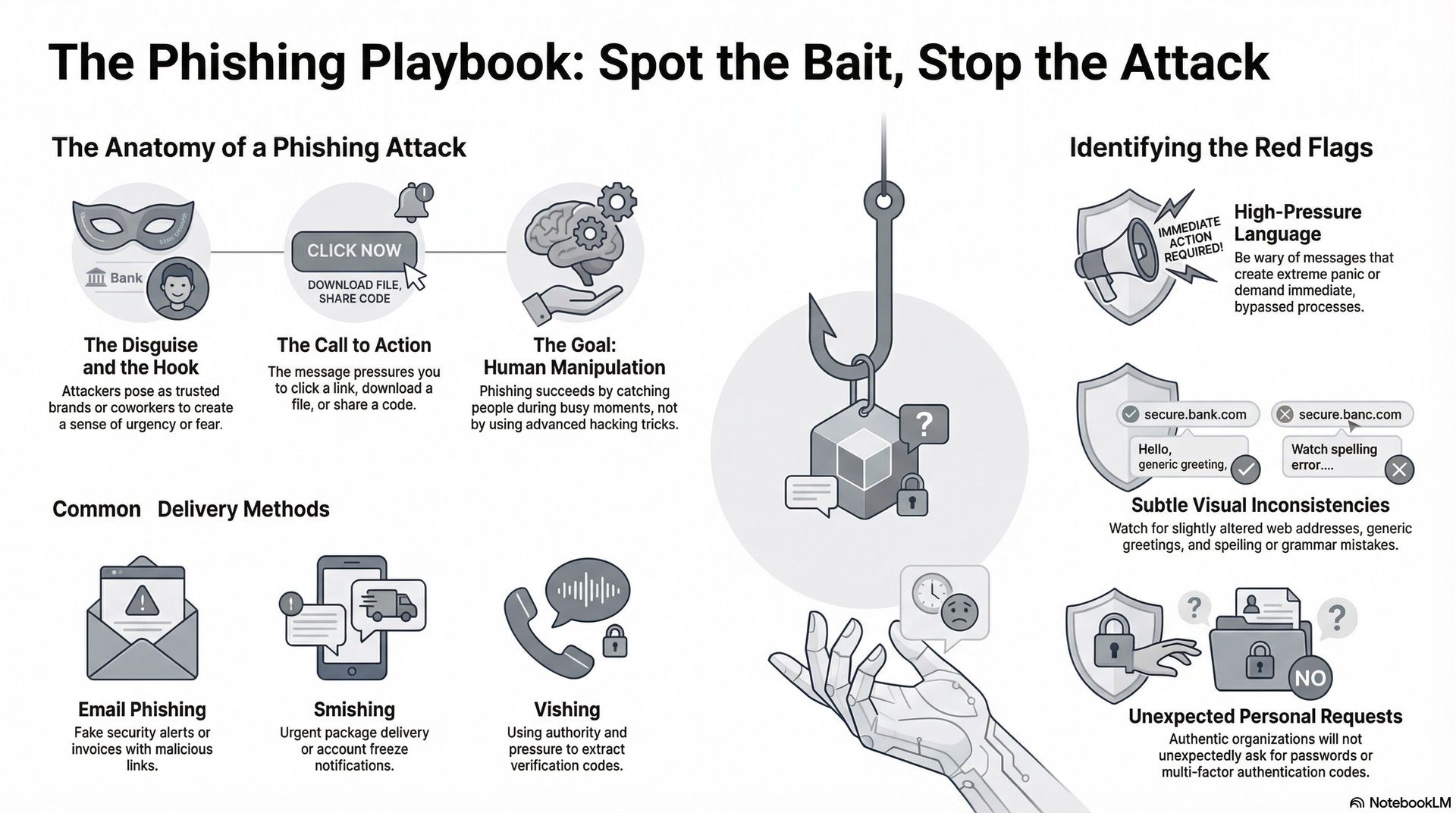
Most phishing attacks follow a simple pattern, even if the details change.
First, the attacker chooses a disguise. This is usually a brand, service, or person you already trust. Banks, mobile carriers, cloud apps, delivery companies, and coworkers are common choices.
Next, they create a message that looks legitimate. That message might come by email, text message, phone call, or even social media direct message. Logos, formatting, and tone are carefully copied.
Then comes the hook. This is the reason you are supposed to act. A suspicious login. A missed delivery. An unpaid invoice. A locked account. Something that creates urgency or fear.
Finally, the attacker asks you to do something. Click a link. Download a file. Reply with information. Enter a code. Send money.
If you follow through, the attacker gets what they want. Your credentials, your data, or your money.
Why Phishing Is So Effective
Phishing works because it exploits how people actually use technology.
Most of us move fast. We scan messages. We multitask. We trust familiar brands. We assume systems are working as intended.
Attackers know this. They design phishing messages to blend into everyday noise. The goal is not to fool experts. It is to catch someone during a busy moment.
Phishing also benefits from scale. Attackers can send thousands or millions of messages at once. Even a tiny success rate can produce real results.
And finally, phishing attacks adapt. When people get better at spotting one trick, attackers shift to another channel or refine the message.
SIM Swap Protection
Get our SAFE plan for guaranteed SIM swap protection.
Common Types Of Phishing
Phishing is not just one thing. It comes in many forms, each designed to fit a different context.
1. Email Phishing
This is the classic version. An email claims to be from a trusted organization and asks you to click a link or open an attachment.
These emails often use subject lines that trigger urgency, like security alerts or payment problems. The link usually leads to a fake website that looks real enough to capture your login details.
2. Smishing
Smishing is phishing via text message.
You might receive a text saying your package could not be delivered, your bank account is frozen, or your phone service needs verification. The message includes a link or a phone number to contact.
Because texts feel more personal and immediate, smishing has become extremely common.
3. Vishing
Vishing is voice phishing, usually done over phone calls.
The attacker may pose as a bank representative, tech support agent, or government office. They often use fear and authority to pressure you into sharing information or reading out a verification code.
4. Spear Phishing
Spear phishing is targeted.
Instead of sending generic messages, the attacker researches you or your organization. The message may reference real coworkers, projects, or recent activity. That makes it feel much more believable.
This type of phishing is often used in business attacks and financial fraud.
5. Clone Phishing
In clone phishing, a real message is copied and slightly altered.
For example, you might receive an email that looks like a legitimate follow up, but the attachment or link has been swapped out for a malicious one.
Because it appears to be part of an existing conversation, it can slip past suspicion.
Monthly
Yearly
What Happens After A Successful Phish
The damage from phishing depends on what the attacker gets access to.
If they steal login credentials, they may:
- Take over email or cloud accounts
- Access financial information
- Reset passwords on other services
- Impersonate you to phish others
If they steal money, the loss can be immediate and difficult to reverse.
In business settings, phishing can lead to larger incidents like data breaches, ransomware infections, or fraud involving large payments.
Even a single compromised account can be enough to cause serious harm.
Signs That A Message Might Be Phishing
Phishing messages are designed to look normal, but there are often subtle red flags.
Pay attention to messages that:
- Create extreme urgency or panic
- Ask for sensitive information unexpectedly
- Use generic greetings instead of your name
- Contain links that look slightly off
- Have spelling or grammar mistakes
- Pressure you to bypass normal processes
No single sign proves a message is malicious, but multiple signs together should raise alarms.
The Role Of Links And Fake Websites
Many phishing attacks rely on fake websites.
These sites are designed to look identical to real login pages. Logos, colors, and layouts are copied closely. The web address is often the only giveaway.
Once you enter your credentials, they are sent straight to the attacker. In some cases, you are then redirected to the real site so you do not even realize what happened.
This is why checking links carefully matters so much.
Phishing And Multi Factor Authentication
Multi factor authentication helps, but it is not a silver bullet.
Some phishing attacks are designed to capture not just your password, but also your one time code. Others trick you into approving a login request you did not initiate.
Attackers are constantly finding ways to work around partial defenses.
Security works best when multiple layers are combined, not when a single feature is treated as a cure all.
Why Mobile Phishing Is Growing Fast
Phones have changed the phishing landscape.
Smaller screens make it harder to inspect links. Notifications feel urgent. Text messages and app alerts blur together.
People also use phones for everything from banking to work authentication. That makes mobile devices a prime target.
Attackers know this and increasingly focus on messages designed for mobile users.
How Phishing Impacts Real People
It is easy to think of phishing as a technical issue, but the impact is very human.
People lose money. Accounts are locked. Identities are stolen. Trust is shaken.
Victims often feel embarrassed, even though the attack was designed to trick them. That embarrassment can delay reporting and make recovery harder.
Understanding phishing is not about blaming users. It is about recognizing how manipulation works so it can be stopped.
How To Protect Yourself From Phishing
There is no single trick that eliminates phishing risk, but good habits make a huge difference.
Slow down when reading messages that ask for action. Verify requests through a second channel when possible. Be cautious with links and attachments. Do not share verification codes with anyone.
On the technical side, use strong unique passwords, enable multi factor authentication where available, and keep devices updated.
Just as importantly, trust your instincts. If something feels off, it probably is.
What To Do If You Think You Fell For A Phish
If you realize you may have responded to a phishing message, act quickly.
Change affected passwords right away. Enable or reset authentication settings. Contact your bank or service provider if financial information was involved.
The faster you respond, the more damage you can prevent.
Reporting the incident can also help protect others.
Why Phishing Is Not Going Away
Phishing continues to evolve because it works.
As long as people use digital services, attackers will try to exploit trust and habit. New tools like automation and AI are making phishing messages more convincing and easier to scale.
That does not mean phishing is unbeatable. It means awareness and layered security matter more than ever.
Conclusion
Phishing is not about sophisticated code or rare exploits. It is about timing, psychology, and trust.
The best defense is understanding how these attacks work and recognizing that anyone can be targeted. Staying alert, slowing down, and verifying before acting go a long way.
When you know what phishing looks like, it loses much of its power.







