SIM Swap Protection
- Lock down your phone number so it cannot be moved behind your back.
- Reduce the fastest path to account takeover: stolen 2FA codes and forced password resets.
- Built for founders, executives, investors, finance teams, and anyone with high-risk digital assets.
Your phone number is no longer just a contact detail. It is a recovery key for email, banking, payroll tools, crypto exchanges, and anything that still treats SMS as identity. If an attacker takes the number, they can often take everything connected to it.
Pricing
Monthly
Yearly
*40GB Priority Data - Speed may slow down after 40GB.
Premium plans with upto 200GB high speed data also available.
Add-ons



The Problem With SIM Swaps
A SIM swap is a mobile line takeover where a criminal convinces a carrier to move your number to a SIM or eSIM they control. The attacker does not need your phone. They need a support channel and enough personal data to sound credible.
If you want the plain-English definition and examples, see What Is a SIM Swap? and how the SIM swap scam typically unfolds.
The FBI reports that Americans lost billions of dollars to investment and crypto-related scams, many of which rely on account takeovers enabled by stolen phone numbers and SMS-based authentication.
Source: FBI IC3.
How A SIM Swap Attack Actually Happens
Most victims picture a hacker breaking in. In reality, the attacker often talks their way in by combining leaked personal data with a believable story and a rushed support channel.
- Keeps your identity and logins intact
- Avoids re-registering on dozens of platforms
- Secures your known number from future attacks
- Instant activation, no waiting for shipping
- No risk of physical SIM card theft or misplacement
- Compatible with most modern devices
.png)
Why Traditional Carriers Fail Here
Carriers are built for speed and volume. Attackers exploit that, especially when the “proof” of identity is the same personal data already floating around online. That is why a number porting scam can succeed even when you have a PIN on file.
Typical Failure Points
Support agents are pushed to close tickets fast.
Verification relies on knowledge-based questions attackers can answer.
Account notes and flags are not consistently enforced across phone, chat, and retail.
Escalation paths are unclear, so urgency becomes a shortcut.
There is no reliable way to confirm the human behind the request under pressure.
What Real Protection Looks Like
Real protection is outcomes-first: prevent unauthorized transfers, control how support can act, and harden recovery so the number cannot be used to steal everything else.
At a high level, SIM Swap Protection adds deliberate friction where it matters and removes the attacker’s ability to shortcut your identity.
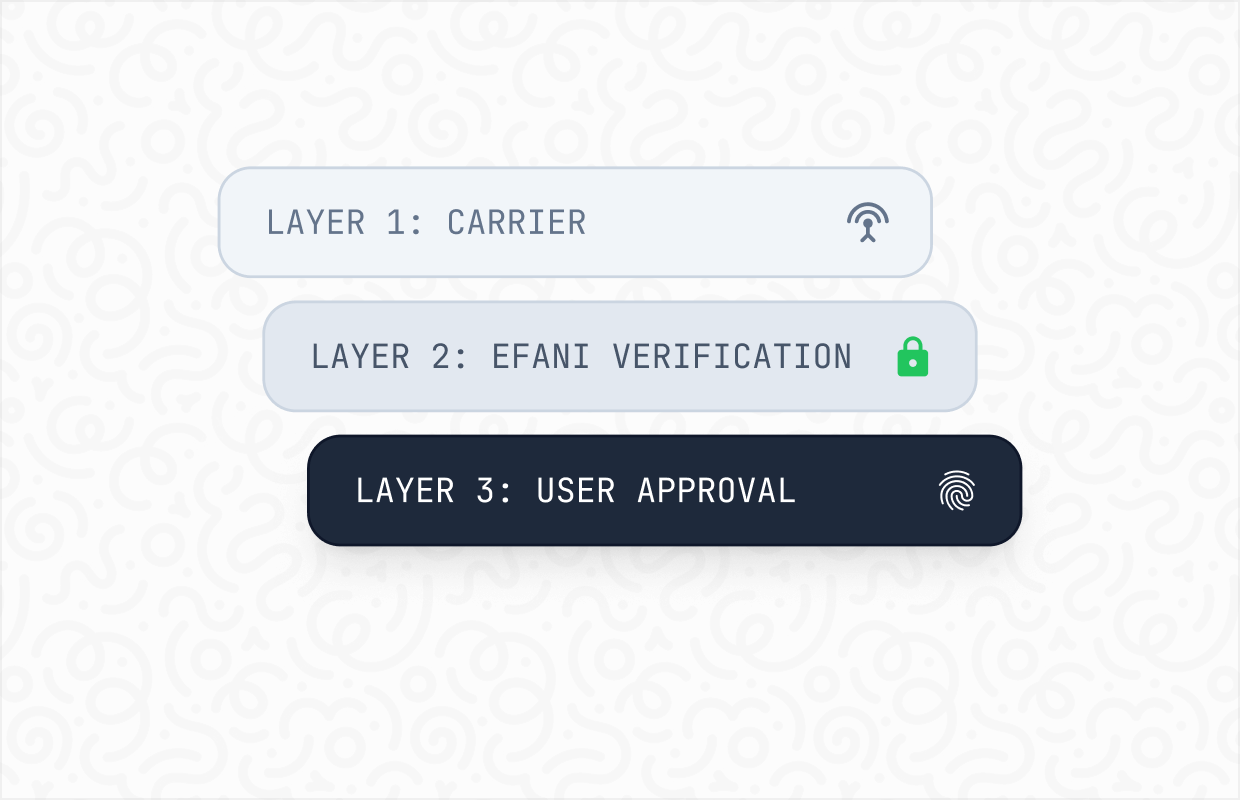
Protection Layers That Matter
- Strong verification for any SIM, eSIM, or transfer request.
- Restricted escalation so high-risk changes are not one rep away.
- Out-of-band validation so a stolen number cannot approve its own transfer.
- Clear recovery workflow when your line shows signs of compromise.
.png)
Prevent The Number Transfer
If the attacker cannot move the number, they cannot intercept your login codes.
Controls That Stop Transfers
- Transfer locks or freezes implemented as policy, not as a note.
- High-assurance verification before SIM or eSIM activation.
- Optional change windows for planned device upgrades.
- Delays or holds when risk signals suggest fraud.
Stop Impersonation At Support
The attacker’s main weapon is believability. Your defense is a workflow where believability is irrelevant.
Controls That Reduce Carrier Impersonation
- Tight access rules for actions that change number ownership.
- Escalation to trained specialists for high-risk requests.
- Consistent enforcement across phone, chat, and retail.
- Identity checks designed for targeted attacks, not casual support calls.
.png)
.png)
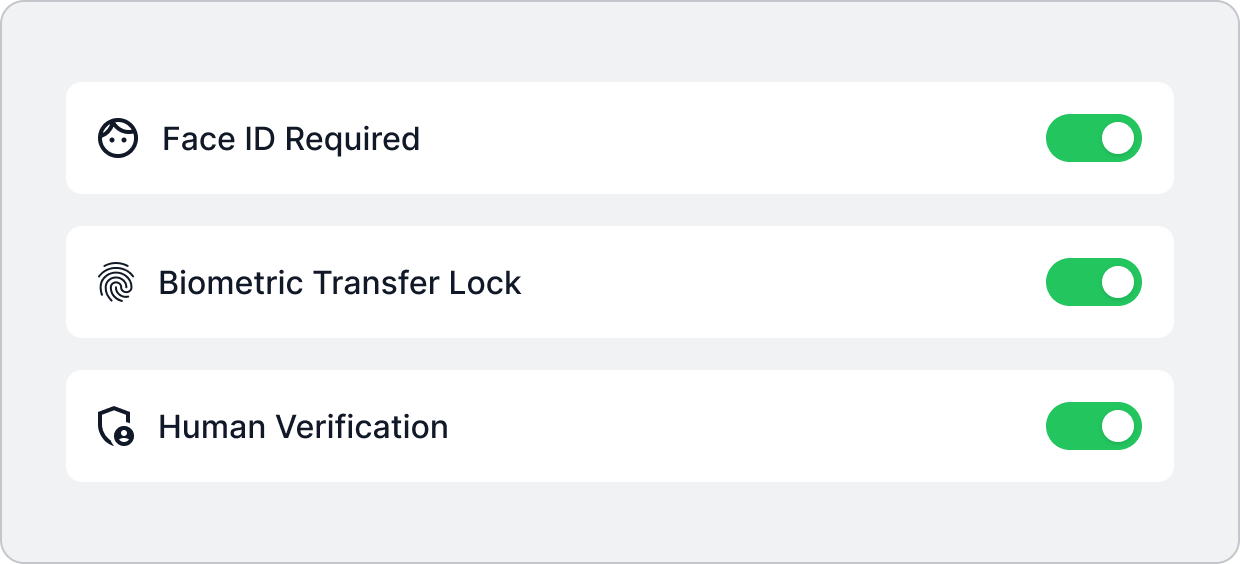
Add Human Verified Controls
Most “security add-ons” fail because they treat this like a settings problem. It is a process problem.
What Human Verification Enables
- Approval paths that cannot be bypassed by social engineering alone.
- Better auditing of what was requested, how it was approved, and by whom.
- A recovery playbook that assumes the attacker will try again
This is where protection becomes real, including resilience against SIM hijacking.
Core Features
Each feature below includes what Efani does, what it stops, and who benefits most.
A hardened process for any SIM, eSIM, or number transfer request.
Stops
- Unauthorized SIM activations
- Surprise number transfers
- Recovery loop abuse
Best For
- Anyone using SMS for account recovery
- Teams with high-value admin accounts
Not every agent, channel, or retail visit should be able to perform high-impact actions.
Stops
- Social engineering against frontline support
- Rushed overrides created by manufactured urgency
- Unauthorized account edits
Best For
- Executives and founders
- Public-facing profiles
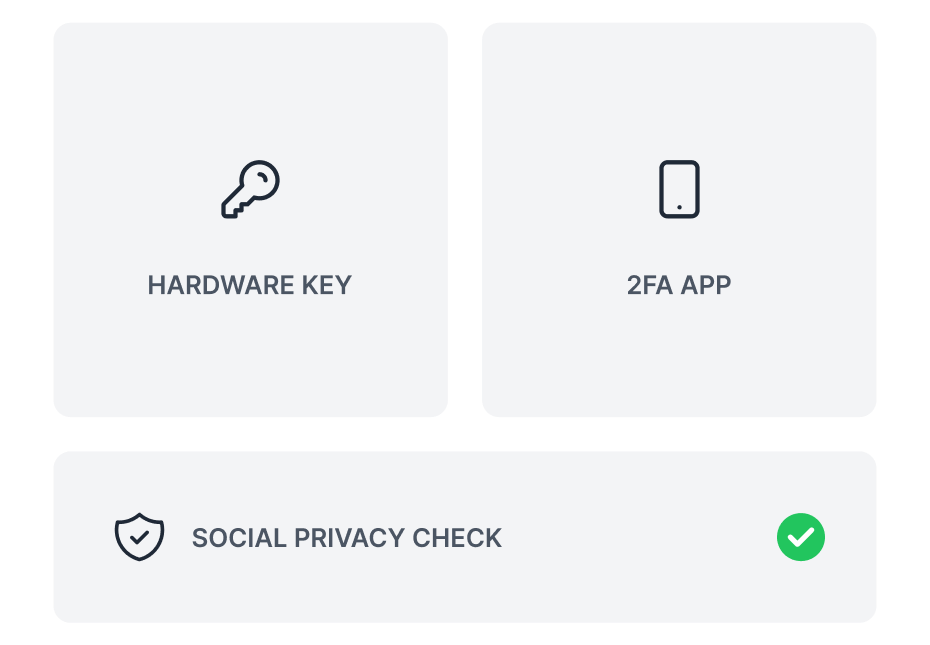
Verification that does not depend on the phone number that might be compromised.
Stops
- Approval via intercepted SMSA
- ttacker-controlled device confirmation
- Fast takeovers during lockout events
Best For
- People who have already been targeted
- Anyone with valuable email and banking access
Lock high-risk changes by default and allow them only under controlled conditions.
Stops
- Late-night number moves
- Opportunistic attacks during travel
- Repeat attempts after a failed social engineering call
Best For
- Frequent travelers
- Users with predictable change needs
Signals that something is wrong, delivered through channels attackers cannot easily suppress.
Stops
- Social engineering against frontline support
- Rushed overrides created by manufactured urgency
- Unauthorized account edits
Best For
- Executives and founders
- Public-facing profiles
A clear plan for what to do the moment service drops or a transfer is suspected.
Stops
- Panic-driven mistakes that worsen a takeover
- Delays that let attackers reset everything
- Confusion across banks, email, and carrier contacts
Best For
- Small teams without internal security staff
- High-profile individuals
Practical help reducing reliance on SMS where it creates the most risk.
Stops
- SMS-based resets for critical accounts
- Account takeover via weak recovery settings
- Repeated OTP interception attempts
Best For
- Anyone modernizing login security
- Organizations standardizing security hygiene

See plan details on Efani Pricing and the onboarding flow on How It Works.
What Our Clients Say About Us
See how Efani users sleep better at night with our secured mobile service.
Devastating to hear this. I switched to @efani secure phone service a few weeks back. You'll never have to worry about sim swap again. Highly recommend.

Yep, switch to @efani ! Excellent service, @haseeb will personally make sure your number is safe and secure
.webp)
Quality of life literally mooning since switching my phone sim to @efani because they somehow find turbo fast internet connectivity globally no matter where you travel first time i’ve been able to trade and sports bet live in the bahamas without feeling like I am on a dial up modem

Who needs efani
This is for people whose number is a dependency, not a convenience. If losing your number for even one hour would create real damage, you are in scope.
Common High-Risk Profiles
System Guardians
Founders and operators who control company email and SaaS admins
Capital Custodians
Finance teams handling payroll, approvals, and banking access
Brand Sovereigns
Creators and publicfigures with monetized accounts
Whaling Targets
Executives who travel and get targeted with urgency pretexts
Frontline Voices
Journalists, activists, and anyone facing targeted harassment
Legacy Links
Anyone with a long-held number tied to years of recovery flows
If Any Of These Are True, You’re A Target
Inbox Vulnerables
Your email can be reset with a text message.
Vault Leaks
Your bank still allows SMS recovery.
Admin Exposures
You rely on SMS for admin logins anywhere.
Use Cases
Short, realistic patterns we see when attackers go after the phone layer first.
Founder Targeted During Fundraising
- Attempt: a “lost phone” story to support, followed by email resets.
- Protection: transfer locking plus specialist escalation blocks the number move.
- Result: the attacker never receives the recovery codes.
Payroll Admin Nearly Locked Out
- Attempt: number moved, then password resets to payroll and bank portals.
- Protection: out-of-band verification prevents the line from authorizing its own transfer.
- Result: payroll stays accessible and approvals stay intact.e recovery codes.
Creator Facing Harassment And Account Resets
- Attempt: social takeover via SMS recovery, then scams sent to followers.
- Protection: high-risk alerts surface the attempt fast, enabling immediate response.
- Result: accounts stay under control and trust is preserved.
Traveler Hit With Sudden “No Service”
- Attempt: fast SIM change timed during transit, then resets across multiple apps.
- Protection: a rapid response playbook reduces containment time and limits damage.
- Result: recovery stays possible before the reset cascade completes.
SIM Swap Prevention Checklist
These steps reduce exposure and make attacks more expensive, even if you do nothing else.

If you are in the middle of an incident, start with Contact Us and keep FAQs open for quick answers.
Put The Risk In Context
Phone-number based takeovers are measurable, not hypothetical.
Over $60 billion in total U.S. cybercrime losses have been reported to the FBI’s Internet Crime Complaint Center from 2020 through 2024.
Source: FBI IC3 Annual Report
Reported U.S. SIM swap complaints rose from 320 cases in 2018–2020 to over 2,100 cases in 2022, a more than fivefold increase in documented phone-based takeovers.
Source: FBI IC3
The FCC warns that port-out scams can let criminals intercept calls and texts, including verification codes used to access accounts.
Source: FCC
Frequently asked questions
Efani combines military-grade mobile security with advanced archiving technology to ensure all communications are securely captured, stored, and easily retrievable in compliance with SEC regulations.
Carriers can reduce risk, but most are optimized for speed at scale. Strong protection usually requires stricter verification and tighter escalation for high-risk actions.
It is better than nothing, but weaker than passkeys, authenticator apps, or hardware keys because the number can be redirected.
Treat it like an incident. Regain control of the line through the carrier’s fraud team, secure email first, then banks, then everything else.
A PIN helps, but it is not a guarantee. Attackers may bypass it through social engineering or inconsistent enforcement across channels.
Often within minutes. Once the attacker receives your texts, they can trigger resets across multiple services quickly.
Assume it could be a takeover until proven otherwise. Borrow another phone, contact your carrier, and lock down email immediately.
Yes. Most people’s data is already exposed somewhere. The goal is to stop “knowledge of you” from being enough to seize your number.
Get Protected
If your number is tied to money movement, admin access, or public reputation, you should not wait for a failed login to act. SIM Swap Protection is most effective before the first attempt, when controls can be set calmly instead of under pressure.
What Happens After You Reach Out
- A short intake on how your number is used (email recovery, banking, payroll, socials).
- A review of your current carrier setup and the most likely bypass paths.
- A recommended rollout plan for your line or lines.
If you want to know why this exists, read the story on Company.
