Trezor vs Ledger: Security Features Compared for Hardware Wallet Protection

Introduction
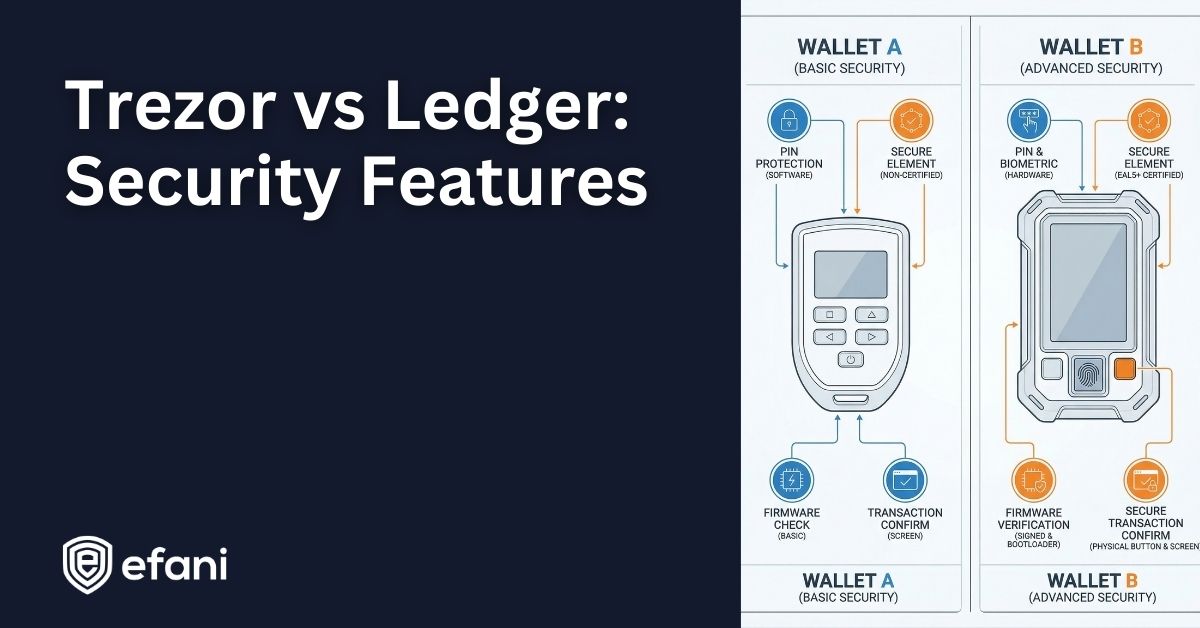
Choosing between Trezor and Ledger is mostly a question of security philosophy and threat model. Both brands are built around the same core promise: your private keys stay on a dedicated device, and every spend requires explicit confirmation on that device’s screen.
But the way they achieve “hardware wallet security” differs in meaningful ways, especially when you look at physical attack resistance, supply-chain defenses, firmware integrity checks, and recovery options.
This guide sticks to concrete mechanisms: Secure Elements, firmware signature verification, attestation, PIN limits, passphrases, and backup systems.
Is your cellphone vulnerable to SIM Swap? Get a FREE scan now!
Please ensure your number is in the correct format.
Valid for US numbers only!
Trezor vs Ledger Hardware Wallet Security Overview
At a high level:
- Trezor security model leans heavily on transparency. Trezor uses open-source firmware and ships devices without pre-installed firmware. On newer “Safe” devices, Trezor adds Secure Elements to harden physical security, enforce PIN limits in hardware, and perform authenticity checks.
- Ledger security model centers on a Secure Element running Ledger OS and a cryptographic attestation system (often experienced as the “Genuine Check”) designed to detect tampering and counterfeit devices when you connect to Ledger’s software.
Neither approach is “objectively best” in every scenario. Trezor’s transparency appeals to people who want maximum auditability and minimal reliance on vendor secrets. Ledger’s model appeals to people who prioritize physical resistance and a hardened root-of-trust anchored in the Secure Element.
Threat Model for Hardware Wallet Security Features
A hardware wallet is only as “secure” as the threats it is designed to resist, and the habits of the person using it. When comparing Trezor vs Ledger security features, it helps to map features to threats:
- Malware on your computer or phone
- Goal: trick you into approving the wrong transaction.
- Defense: verify address and amount on the device screen before confirming.
- Goal: steal your recovery phrase or trick you into signing something you do not intend.
- Defense: never type recovery words into apps, websites, or “support” chats.
- Physical theft of the device
- Goal: brute-force the PIN or extract keys with advanced hardware attacks.
- Defense: Secure Element protections, enforced PIN limits, passphrase.
- Supply-chain tampering
- Goal: alter the device before you ever unbox it.
- Defense: authenticity checks, firmware integrity checks, seals or attestation.
- Backup compromise
- Goal: steal your backup or a share of it.
- Defense: strong backup hygiene, multi-share backups, and passphrase discipline.
The “best” device depends on which of these you treat as realistic for you.
Trezor Security Features
Trezor’s security story depends heavily on which model you’re talking about.
The brand spans older devices (Model One, Model T) and newer “Safe” models (Safe 3, Safe 5, Safe 7) with additional physical security layers.
1. Trezor Firmware Integrity and the “Ships Without Firmware” Approach
A distinctive Trezor feature is that devices are distributed without firmware installed. During setup, you install firmware through Trezor Suite, and the setup flow checks whether firmware is already present. If firmware is detected on a brand-new device, Trezor’s guidance is not to use it.
Once firmware is installed, Trezor describes a bootloader-based verification process:
- The bootloader verifies the firmware signature when you connect or power the device.
- Trezor Suite only accepts the device if installed firmware is correctly signed by SatoshiLabs.
- If unofficial firmware is installed, the device shows a warning.
2. Trezor Secure Element Security in the Safe Line
With the Safe line, Trezor adds Secure Elements to strengthen resistance against physical attacks. Trezor describes three key Secure Element roles in these devices:
- Hardware-enforced PIN protection (defending against brute-force attempts on a stolen device)
- Device genuineness verification via a certificate stored in the Secure Element
- Secure randomness contribution during seed creation (additional entropy source)
Trezor also explains a specific key-protection flow: the Secure Element holds a secret used with your PIN to protect keys stored on the main chip, and it releases that secret only after a correct PIN entry.
3. Dual Secure Elements in Trezor Safe 7
Trezor Safe 7 is positioned as a dual Secure Element device using OPTIGA Trust M (V3) and TROPIC01.
Trezor states they work together to verify authenticity, enforce PIN limits, and contribute secure randomness for wallet backup.
4. Trezor PIN Security Features, Attempt Limits, and Delays
Trezor’s PIN system includes an attempt limit and increasing delays between attempts:
- Safe 7 resets after 10 incorrect PIN attempts.
- Other Trezor models reset after 16 incorrect attempts.
Older models (Model T and Model One) do not have hardware-enforced rate limiting in the same way a Secure Element can enforce it, which changes the physical-attack story compared to the Safe line.
5. Trezor Wipe Code as an Additional Physical Security Feature
Trezor offers a wipe code feature: a secondary code that, when entered, wipes the device. It is a niche option, but it can matter for certain physical threat models.
6. Trezor Passphrase Security and On-Device Entry
Passphrases add a second secret on top of your recovery phrase, creating additional wallets that require the passphrase to access. Where the passphrase is entered matters:
- Safe 7, Safe 5, and Model T support on-device entry via touchscreen.
- Safe 3 supports on-device entry using device buttons.
- Model One does not support on-device entry; you type it on the connected computer or phone.
7. Trezor Anti-Tamper Packaging and Authenticity Checks
Trezor combines physical tamper-evidence with software checks.
For Safe 3, Trezor describes a tamper-evident holographic seal over the connector, and it emphasizes authenticity checks during setup, including Secure Element checks on Safe devices.
SIM Swap Protection
Get our SAFE plan for guaranteed SIM swap protection.
Ledger Security Features
Ledger’s security design is Secure Element centric across its product line. Ledger devices use a Secure Element plus Ledger OS, and Ledger builds significant security logic around attestation and secure channels.
1. Ledger Secure Element Security and Certification Levels
Ledger states different devices use Secure Elements with different Common Criteria certification levels, including EAL5+ and EAL6+. Ledger Nano X is described as EAL5+, while Ledger Nano S Plus and Ledger Stax are described as EAL6+.
2. Ledger OS Security Features and App Isolation
Ledger uses a custom operating system (Ledger OS, historically called BOLOS).
Apps are designed to operate in constrained environments, while sensitive operations are mediated by the OS to keep secrets protected.
3. Ledger Attestation, Genuine Check, and Root of Trust
A core Ledger security feature is attestation: proving the device is genuine and not running tampered firmware.
Ledger describes factory-provisioned device keys and certificates that are later used to establish a secure channel and pass genuineness checks when connecting to Ledger software.
4. Ledger PIN Security and Factory Reset Behavior
Ledger’s PIN model is strict: PIN length is typically 4 to 8 digits, and after three incorrect PIN attempts the device resets to factory settings.
This is a strong defense against brute force after theft, but it raises the stakes of protecting your recovery phrase.
5. Ledger Passphrase Security Options
Ledger supports BIP39 passphrases with two main modes:
- Temporary passphrase sessions that end when you disconnect.
- Passphrase attached to a PIN, where a secondary PIN unlocks a passphrase wallet.
6. Ledger “Secure Screen” Claims on Touchscreen Devices
Ledger emphasizes that on its secure touchscreen devices, the screen is driven by the Secure Element so what you see on the device is what is actually being signed.
Monthly
Yearly
Trezor vs Ledger Security Features
Trezor’s Safe line uses Secure Elements as a hardening layer in a transparency-first design, including PIN enforcement, genuineness checks, and a protected secret that helps encrypt keys stored on the main chip. Ledger’s design is more deeply anchored in the Secure Element, with Ledger OS and attestation built around it.
Both approaches target the same outcomes: make physical extraction harder, enforce PIN attempt limits, and prevent tampered firmware from silently taking over.
The meaningful differences are how much you prioritize public auditability versus Secure Element-rooted trust chains and attestation.
Trezor Shamir (SLIP39) vs Ledger Recover and Recovery Key
Backups are where most people fail in real life. The best device security can be undone by a recovery phrase stored in a photo gallery, a cloud note, or a compromised metal backup.
Trezor Backup Standards: BIP39 and SLIP39
Trezor uses standardized formats for backups:
- BIP39 for 12 or 24 words
- SLIP39 for 20 words (Trezor’s newer “wallet backup” standard)
Trezor Multi-Share and Shamir Backup Security Features
Trezor’s Shamir and multi-share ecosystem splits recovery into multiple shares:
- Shamir backup can generate up to 16 recovery shares.
- Multi-share backup supports 1 to 16 shares with a recovery threshold (X-of-Y).
- Multi-share backup can be used on Safe 7, Safe 5, Safe 3, and Model T.
A crucial point is that “upgrading” does not automatically eliminate risk if older backups remain valid and are later compromised.
Ledger Recovery Options
Ledger’s baseline backup is the 24-word Secret Recovery Phrase (SRP), with additional recovery-oriented options:
- Ledger Recover is an optional paid subscription built around encrypted, fragmented recovery with identity verification.
- Ledger Recovery Key is positioned as an offline, PIN-protected backup card that stores a copy of the SRP.
These options can reduce the chance of catastrophic loss from mishandling paper words, but they also introduce new operational choices and trust models.
Trezor Open Source vs Ledger 95% Open Source
Transparency is part of security, but it is not the same thing as security. Still, it matters for trust and independent verification.
Trezor frames transparency as core to its model and says it chose Secure Elements to support public review without NDA restrictions, with Safe 7 adding TROPIC01 as an open and auditable element.
Ledger publicly argues it cannot be fully open source due to Secure Element ecosystem constraints, describing itself as 95% open source.
What Matters for Trezor vs Ledger
This is where features become practical decisions.
If Your Main Threat Is Malware on Your Computer or Phone
Both devices protect you by keeping keys on-device and forcing on-device confirmation.
The differentiator is how clearly you can verify what you are signing on the hardware screen, and whether advanced features like passphrases are entered on-device.
If Your Main Threat Is Physical Theft Plus a Motivated Attacker
This is where Secure Elements and enforced PIN attempt limits dominate.
Ledger resets after three incorrect PIN attempts, while Trezor Safe devices enforce PIN verification with a Secure Element and reset after a larger number of failed attempts.
If Your Biggest Risk Is Losing Your Backup
Trezor’s multi-share approach is designed to reduce single points of failure, while Ledger offers optional recovery services or a recovery card to reduce backup handling mistakes.
No recovery system beats good backup hygiene and secure storage.
Which Hardware Wallet Is More Secure for You
Here is a practical way to decide that stays grounded in security features.
Choose Trezor If You Prioritize These Security Features
- You want strong transparency and an audit-friendly security posture.
- You want SLIP39 and multi-share backup options as a first-class recovery strategy.
- You want on-device passphrase entry on newer models (Safe 3, Safe 5, Safe 7).
- You are specifically considering the newer Safe line with Secure Elements rather than older models without that hardware layer.
Choose Ledger If You Prioritize These Security Features
- You want a Secure Element-centric architecture across the line, with a strong focus on attestation and genuineness checks.
- You want a strict PIN attempt policy that factory-resets after three incorrect tries.
- You want optional recovery tooling like Ledger Recover or the offline Ledger Recovery Key card.
- You like the Secure Element-driven secure screen concept on touchscreen devices.
Conclusion
Trezor vs Ledger security features are not a simple winner takes all comparison. Ledger’s security model is rooted in Secure Element hardware, Ledger OS isolation, and cryptographic attestation.
Trezor’s security model emphasizes transparency, signed firmware verification, and in the Safe line, Secure Elements that enforce PIN limits and verify authenticity.
FAQs
Is Trezor or Ledger More Secure Against Physical Hacking?
It depends on the model and your threat level, and modern Secure Element devices are the relevant comparison. Ledger resets after three incorrect PIN attempts, while Trezor Safe devices enforce PIN limits via Secure Elements with higher attempt thresholds. If physical theft is your top risk, prioritize strong PINs, modern hardware, and a passphrase for a second layer.
Do Trezor Devices Really Ship Without Firmware, and Why?
Yes, Trezor’s setup model is built around installing firmware during first use and checking for unexpected preinstalled firmware. The security goal is to reduce supply-chain risk by making “already configured” devices a red flag. If anything looks off during setup, stop and verify the device’s authenticity before proceeding.
How Does Ledger Verify a Device Is Genuine?
Ledger uses attestation built from factory-provisioned device keys and certificates to pass genuineness checks. When you connect to Ledger software, the device proves it has the correct protected keys and has not been replaced by a clone. If attestation fails, the workflow is designed to block device use rather than silently accept risk.
How Many PIN Attempts Do You Get on Trezor vs Ledger?
Ledger devices typically reset after three incorrect PIN attempts. Trezor Safe 7 resets after 10 incorrect attempts, while other Trezor models commonly reset after 16 incorrect attempts. Your recovery phrase is the real backstop, so protect it as if it is the wallet.
Is Entering a Passphrase Safer on Trezor or Ledger?
Passphrase safety is mostly about where it is entered and whether a compromised host can capture it. Trezor Safe models support on-device passphrase entry, while Model One requires typing it on the connected device. Ledger supports temporary passphrases or passphrases attached to a PIN, which can be safe if you manage the workflow carefully.
What Is Trezor’s Multi-Share Backup and How Is It Different From a Normal Seed Phrase?
Multi-share backup splits recovery into multiple shares, reducing single points of failure if one copy is lost or stolen. You can choose a threshold scheme, so an attacker with only one share cannot necessarily recover the wallet. It adds setup complexity, so it is best when you can store shares in separate secure locations long-term.
What Is Ledger Recover and Does It Weaken Ledger Security If You Do Not Use It?
Ledger Recover is an optional paid service that uses encrypted fragmentation and identity verification to help recover access. If you do not enable it, your device still relies on your seed phrase and normal self-custody practices. Whether to use it depends on your trust model and your risk of losing traditional backups.







