Crypto Security
March 11, 2026
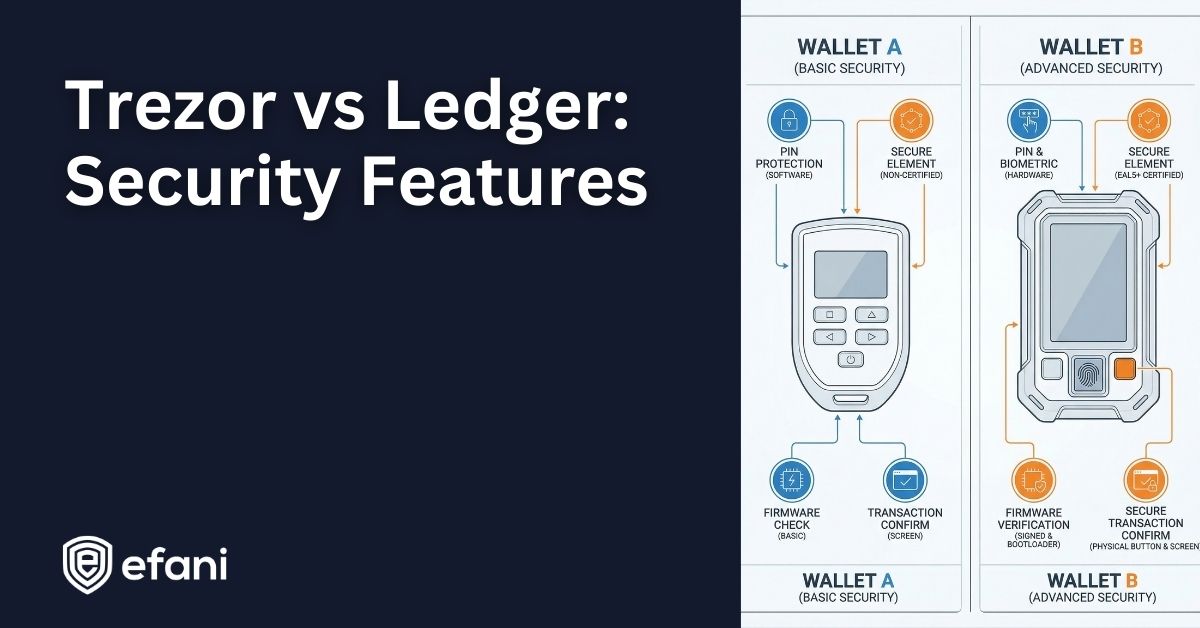
Trezor vs Ledger: Security Features Compared for Hardware Wallet Protection
A detailed comparison of Trezor and Ledger hardware wallet security. Learn how Secure Elements, firmware verification, PIN protection, passphrases, and recovery systems differ between the two devices.
.jpg)
Crypto Security
January 16, 2026
Ledger Security Breaches and Incidents: Full History From 2018 to 2026
A complete, fact checked timeline of Ledger security breaches, data leaks, and trust controversies from 2018 to 2026, and what they actually mean for hardware wallet users today.

Crypto Security
January 16, 2026
Ledger Data Breach January 2026: What Happened, What Was Exposed, and Why It Matters
A detailed breakdown of the January 2026 Ledger data breach involving Global-e, what customer data was exposed, why crypto users are alarmed, and how this incident fits into Ledger’s long breach history.

Crypto Security
January 4, 2026
Cryptocurrency Trends: Five Predictions For The Coming Year (2026)
From institutional capital and stablecoin regulation to AI-driven DeFi and Bitcoin yield, these five trends explain how crypto is maturing, and why security and infrastructure matter more than ever.

Crypto Security
November 7, 2025
The Complete Crypto Mobile Security Audit Checklist
A step-by-step mobile security checklist for crypto investors. Learn how to secure your phone, lock your carrier, and protect wallets from SIM swaps with Efani’s insured crypto mobile plan.

Crypto Security
August 22, 2025
How to Secure Your Crypto with Tangem Wallet and Protect Your Family’s Future
Plan for the unexpected. Learn how Tangem Wallet’s 3-card system makes crypto inheritance safe, simple, and accessible for your loved ones.
